“EternalBlue” is a technique that exploits vulnerabilities in the Windows operating system. It targets older versions such as Windows XP, Windows Server 2003, and Windows 7. The EternalBlue exploit attack is based on the following principles:
EternalBlue Exploit Vulnerability
EternalBlue exploits a security flaw in the implementation of the Microsoft SMB (Server Message Block) v1.0 protocol. Specifically, the vulnerability exists in the Windows Server service, allowing attackers to remotely execute code by sending specially crafted SMBv1 requests.
EternalBlue Exploit Attack Process
Scanning Targets: Attackers initially scan the network for systems running vulnerable versions of Windows to identify potential targets.
Sending Malicious Packets: Once a target is identified, attackers send specially crafted SMBv1 packets containing malicious code.
Exploiting the Vulnerability: Upon receiving the malicious packet, the target system, due to the vulnerability, writes and executes the malicious code in its memory.
Gaining System Access: Successful execution of the malicious code grants attackers remote access to the target system, enabling them to execute arbitrary commands or install malware.
EternalBlue Attack Impact and Spread
EternalBlue attacks spread rapidly, especially in systems where patches released by Microsoft were not promptly installed. Because the attack exploits vulnerabilities in the operating system rather than relying on user actions, it can spread widely and cause significant damage.
The vulnerability was famously leveraged in global ransomware attacks, such as the WannaCry ransomware incident in 2017, which resulted in widespread system disruptions and data loss.
How to Detect EternalBlue Exploit via Sax2 IDS
Sax2 IDS is a professional intrusion detection software, the following is an example of how to create a Sax2 security policy to detect EternalBlue.
Step1. Click the “Policy” button on the top of the main menu to display the policy management window, and then derive a policy set (note: the system policy set cannot be modified), please see the following figure:

Step 2. Double-click the derived policy set or select the derived policy set, and then click the Edit button to display the policy list window, as shown in the following figure

Step 3. Switch to the “Custom” page, select the “Backdoor” group, and then click the “New” button to create a new security policy. For detailed settings, please refer to the following image.
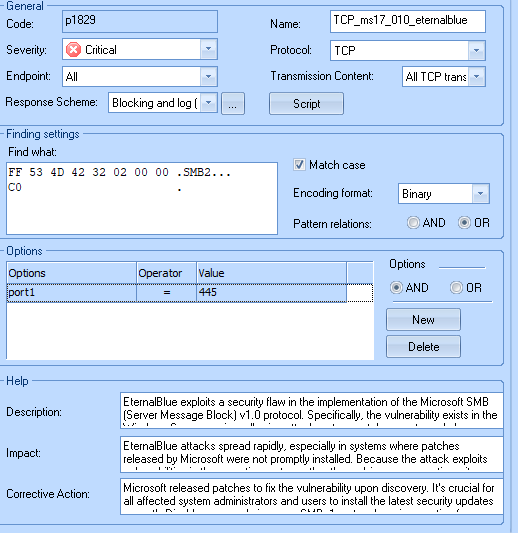
The key to creating a policy is to analyze and find the signature of the attack, from the above diagram we can see that the characteristics of Eternal Blue are “FF 53 4D 32 02 00 00 CO”, read this article “Packet-level Analyze NSA’s EternalBlue Exploit via Wireshark” to understand the analysis process. This article also describes how to make sort rules to detect EternalBlue.
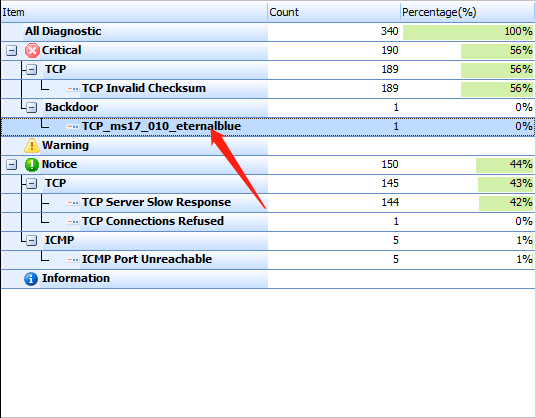
Step 4. After saving and applying the newly created security policy, and then launching an attack, I can see that Sax2 detected the intrusion, see the image below:
Mitigation and Prevention
- Microsoft released patches to fix the vulnerability upon discovery. It’s crucial for all affected system administrators and users to install the latest security updates promptly.
- Disable or upgrade insecure SMBv1 protocol versions, opting for more secure alternatives like SMBv2 or SMBv3.
- Regularly update systems and security software, deploy network security measures such as firewalls, intrusion detection systems (IDS), and endpoint security controls to prevent future exploitation and attacks.
Conclusion
The exploitation of the EternalBlue vulnerability and related attack incidents highlight the importance of timely system updates and maintenance to protect networks and computing devices from potential security threats.